What Is Single Sign On Spring Boot Youtube
Security
Single Sign-On with Kerberos using Jump…

I would presume that almost of yous had known about Single Sign-On and Kerberos, simply you don't know how to implement the Kerberos for Single Sign-On. Let's understand the title phase by phase. What Single Sign-On ways is the access to all accounts with using one User Id and Password. Kerberos is an hallmark protocol. Spring is, by far, the well-nigh popular framework for application development in the Coffee ecosystem. This is my 17th article in Medium.
What is Unmarried Sign-On (SSO)
Nowadays, people apply many software applications. In well-nigh of the web applications, the user needs to create a profile to get started. Therefore, the user should remember each accounts' User Id and password. This is an inconvenience for the user. Thus, developers have come up up with a mechanism called "Single Sign-On". You already know what is meant by Unmarried sign-on. At that place are a lot of protocols that provide services to access related, contained software applications such as Kerberos, SAML, OpenID, etc . SSO is more often than not achieved by Lightweight Directory Access Protocol (LDAP) and stored LDAP databases on (directory) servers . Conversely, there exists a mechanism called "Unmarried Sign Off". Single Sign Off means that if the user logs Out of i application then, all the sign-in applications of the specified user volition get to Log Out likewise.

Kerberos
Co-ordinate to Greek mythology, Kerberos (Cerberus) was a three-headed canis familiaris that guarded the underworld to prevent the expressionless from leaving. Kerberos was adult past the Massachusetts Institute of Technology (MIT) for project Athena in the early 1980s. Plenty with the history and meaning, now let's get into more than technically in-depth. Kerberos is a Network Hallmark Protocol. Kerberos is used in the c lient-server model Architecture systems. This protocol prevents eavesdropping and replay attacks . Kerberos builds on symmetric-key cryptography .

Kerberos is designed for 2 purposes. They are security and hallmark . Suppose a client wants to access a Postal service server, only with Kerberos, the client must be verified through a trusted third party and this third party known every bit " Key Distribution Center ( KDC )". KDC includes two servers. They are an Hallmark Server ( Equally ) and a Ticket Granting Server ( TGS ). If a client wants to access the Mail Server, then these post-obit steps will be executed in Kerberos.
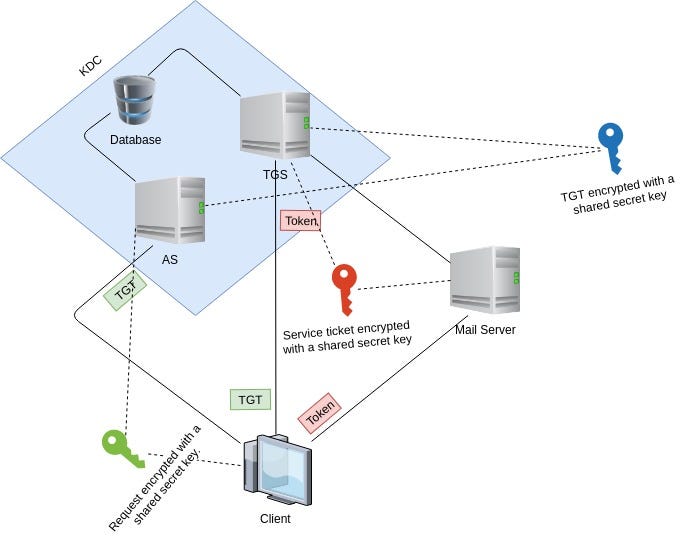
Step1: The client sends a request to the Authentication Server (AS) such equally "my user ID is so and and so, and I need a ticket to the mail server", something like this. The client request is partially encrypted by a hush-hush key . That fundamental is the client password. The client never sends his/her password over the unsecured network. The client uses his/her password as an encryption key. When the AS gets the client'southward request, it will retrieve their countersign in the database based on userID, and utilize the client password every bit a fundamental to decrypt the client's request. The client'southward password is a hole-and-corner shared fundamental betwixt the Authentication Server and the customer. You lot encounter, the Kerberos pattern is so smart. If the password from the database can de-encrypt the asking, this means the user is provided with a right combination of his password and his userID. This is how the user is verified. Afterwards verifying the client, Authentication Server sends back a ticket chosen " Ticket Granting Ticket ( TGT )", encrypted with another hugger-mugger key.
Step2: After the client gets the encrypted TGT, the client sends it to Ticket Granting Server, along with the client's request such as "I desire to access the Mail Server". When the TGS gets the TGT, it decrypts the ticket with the hole-and-corner key shared with the Authentication Server. Then TGS issues the customer a token , which is encrypted with another secret primal. This third hugger-mugger key is shared between TGS and the mail server. Then the client sends the token to the Mail Server.
Step3: When the Mail Server gets the token, information technology decrypts the token with the underground fundamental shared with TGS. The Mail Server allows the client to utilise its services for a certain flow co-ordinate to the token. The token is similar a motion-picture show ticket with which a person can go to a theatre to bask a particular movie at a specific time on a certain twenty-four hour period.

In the in a higher place diagram, you can see all the communications between the different parties involved a secret key. For example, the customer and the Authentication Server shared a secret key, which is the client's password. Hallmark Server and Ticket Granting Server shared a hole-and-corner fundamental. Ticket Granting Server and the Mail Server share a secret cardinal.
Spring Framework
Here I won't explain about Spring framework. Here I am going to depict why we want to use Jump for Single Sign-On with Kerberos.
- Configuration support to Java Programming Language.
- Portable.
- Comprehensive support to tasks like authorisation and hallmark.
- Servlet API integration.
- Bound MVC integration.
- CSRF protection.
- Protection confronting some common tasks.
Implementation
Hither let me first describe the implementation of KDC and Client awarding and server awarding.
KDC
Commencement, we run KDC to get TGT.
Client Application
Hither I've created a simple client grade. You tin use it as a template.
Bound boot awarding using a Rest template to make calls to an external Residual API Therefore, we are going to use KerberosRestTemplate instant of that Remainder template.
Server Application
Here I used Spring security
Conclusion
In this article, I mentioned how to utilize spring kick to Single Sign-On with Kerberos. I've just scratched the surface here and if yous want to dive deeper, Cheque its RFC or official documentation page. If you want to run across what is internally happen in cadre Java use this Oracle link. As usual, the lawmaking can be institute on my GitHub page.
References
- Baeldung. Learn Spring Security. [online]. Available: https://www.baeldung.com/larn-jump-security-form [Accessed viii Aug. 2019].
- thekspace.com. Kerberos and SPNEGO. [online] Available: http://www.thekspace.com/dwelling/component/content/article/54-kerberos-and-spnego.html [Accessed vii Aug. 2019].
- DataFlair. Jump Security Tutorial Step By Step — Case & Advantages. [online]. Available: https://data-flair.training/blogs/leap-security-tutorial/ [Accessed 9 Jul. 2019].
Thank you for reading this far. If you enjoyed this post, please share, comment, and printing that 👏 a few times (up to 50 times). . . Maybe it will help someone.
Follow me on Twitter and Medium if you're interested in more than in-depth and informative write-ups like these in the hereafter!
Source: https://medium.datadriveninvestor.com/single-sign-on-with-kerberos-using-spring-bff3eb835bc8
Posted by: catalanoource1962.blogspot.com

0 Response to "What Is Single Sign On Spring Boot Youtube"
Post a Comment